Part 2 of 2 articles to unit test Kafka Streams application. In the second part, I talk about testing Processor API by using MockProcessorContext as well as how to test Processor Scheduler with two types of Punctuator: STREAM_TIME and WALL_CLOCK.
Transform Passion into Knowledge
Part 2 of 2 articles to unit test Kafka Streams application. In the second part, I talk about testing Processor API by using MockProcessorContext as well as how to test Processor Scheduler with two types of Punctuator: STREAM_TIME and WALL_CLOCK.
This is part 1 of 2 articles to unit test Kafka Streams application. The first part talks about testing DSL transformation, stateless and stateful, including joining and windowing.

Painless is a simple, secure scripting language designed specifically for use with Elasticsearch. It is the default scripting language for Elasticsearch and can safely be used for inline and stored scripts.
https://bit.ly/2TRuUNj
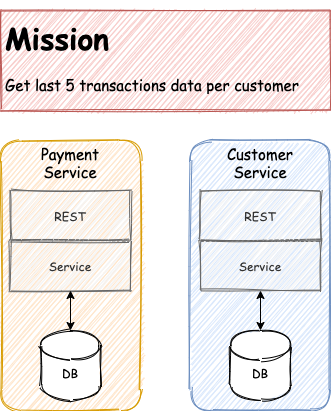
A microservice architecture is all about transferring data from one service to another.
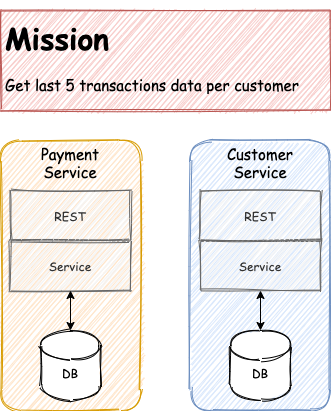
A microservice architecture is all about transferring data from one service to another.

Yet another Kafka feature, which is Kafka Streams, allow us to join two streams into one single stream. Kafka streams provide one-to-many and many-to-one join types.

Sensitive data always need to be handled with extra careful. Thus, in some cases, we need to encrypt before delivering message to Kafka topic.

After we secure Kafka Broker and Zookeeper with SASL/SCRAM, it is time for client (Java + Spring) to connect to secured Kafka.

Overview When I decided to include Apache Kafka as one of our technology stack, I never imagine the demand would be this huge. At first, my requirements were only two things. Something faster than ActiveMQ […]