
Introduction Recently, I was assigned to reduce technical debt in an existing project. One of the keys highlighted technical debt is how low the code coverage is. Therefore, our priority is to increase code coverage […]
Transform Passion into Knowledge

Introduction Recently, I was assigned to reduce technical debt in an existing project. One of the keys highlighted technical debt is how low the code coverage is. Therefore, our priority is to increase code coverage […]
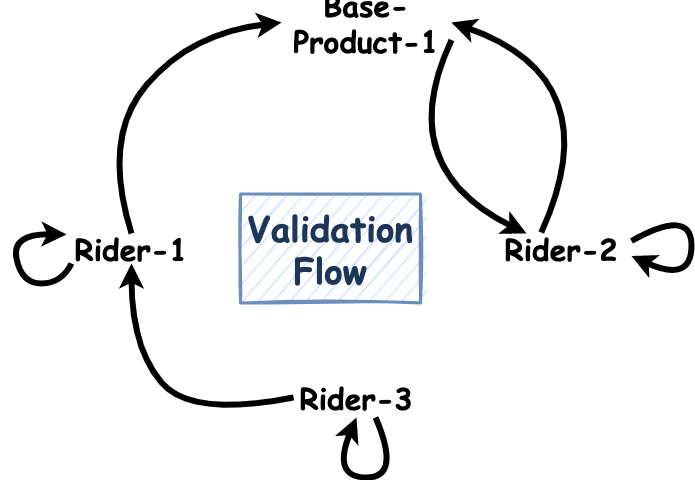
When you dealing with inter-dependencies (or circular dependencies) rules between components, you can consider to use Intercepting Filter Design Pattern to solve your problems.
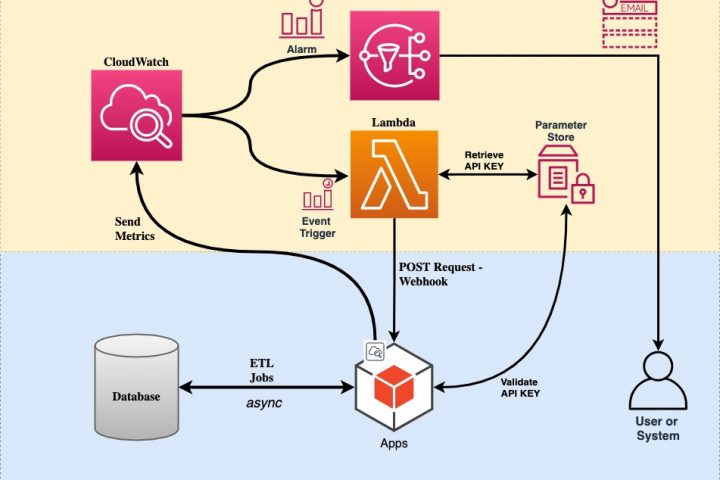
After we have a blueprint for our solutions in part 1, now it is time to implement it into code. We use AWS Cloud Development Kit (CDK) as Infrastructure as a Code and Spring Boot as our custom job implementation.
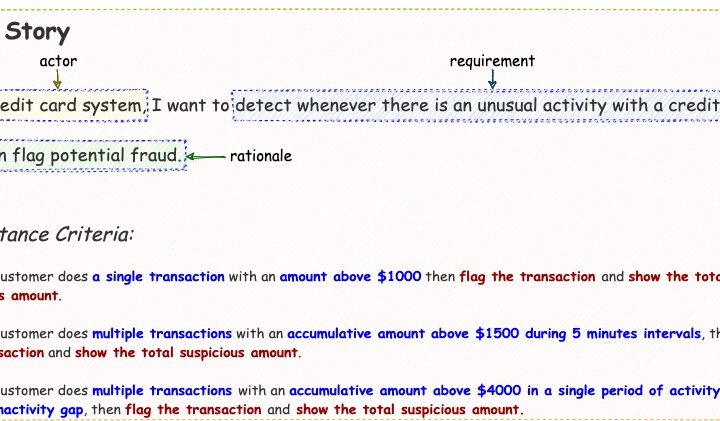
Part 2 will talk about mapping the Gerkhin feature file into Cucumber Step Definition and its implementation using Kafka Streams.
This is part 1 of 2 articles to unit test Kafka Streams application. The first part talks about testing DSL transformation, stateless and stateful, including joining and windowing.

Data privacy and security became critical nowadays. Thus, we need to isolate database credentials and make it transparent to our applications/services.
Overview In this article, I will provide a simple example to secure REST example by using Oauth2. I will not explain what Oauth2 protocol is all about in detail. In short, to implement this authorization […]

One of the main component of micro service architecture is service discovery (SD). So far in this blog I mentioned two tools for service discovery, which are Eureka and Consul. But if you may notice, whenever I used spring-cloud framework, I always choose Eureka. On the other hand, I pick consul when I talked about Golang.
Overview In this article, I will revisit a little bit my old article, but still valid, regarding monitoring your services. As you can see in my previous article, I wrote about monitoring service in Go […]
Overview In Java world, when it comes to database connectivity, there are two main approaches to deal with. First one is direct JDBC connection by using DriverManager. The other one is by using data source. […]